Abusing Exceptions for Code Execution, Part 1
Por um escritor misterioso
Last updated 19 setembro 2024
A common offensive technique used by operators and malware developers alike has been to execute malicious code at runtime to avoid static detection. Often, methods of achieving runtime execution have focused on placing arbitrary code into executable memory that can then be executed. In this article, we will explore a
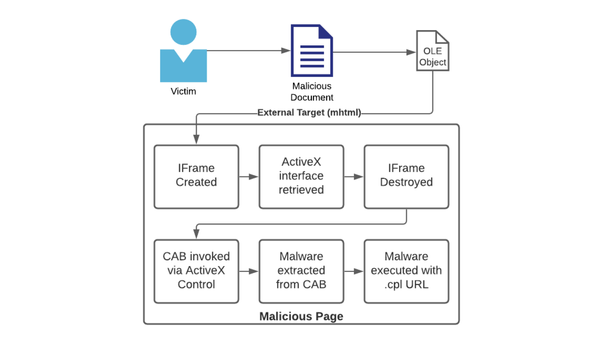
A common offensive technique used by operators and malware developers alike has been to execute malicious code at runtime to avoid static detection. Often, methods of achieving runtime execution have focused on placing arbitrary code into executable memory that can then be executed. In this article, we will explore a new approach to executing runtime code that does not rely on finding executable regions of memory, but instead relies on abusing existing trusted memory to execute arbitrary code.
A common offensive technique used by operators and malware developers alike has been to execute malicious code at runtime to avoid static detection. Often, methods of achieving runtime execution have focused on placing arbitrary code into executable memory that can then be executed. In this article, we will explore a new approach to executing runtime code that does not rely on finding executable regions of memory, but instead relies on abusing existing trusted memory to execute arbitrary code.
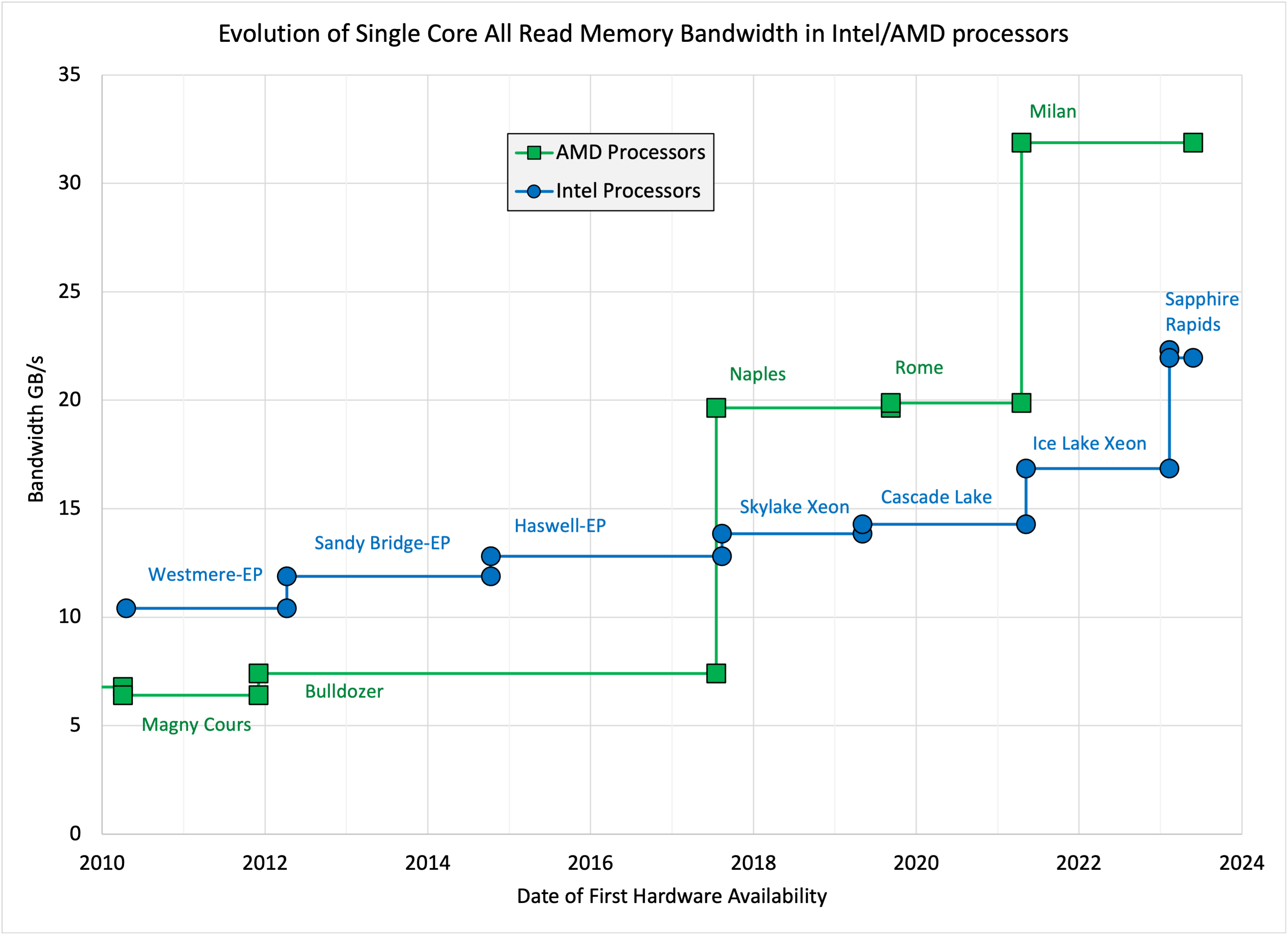
John McCalpin's blog » STREAM benchmark
Abusing Exceptions for Code Execution, Part 1

mTLS: When certificate authentication is done wrong - The GitHub Blog
Exploitation Protections From Old To Bleeding Edge pt 1, by Edward Amaral Toledano, stolabs

A Memoir of My Former Self

Opioid Prescribing for Chronic Pain: Case Studies and Best Practices
How to use ChatGPT as a learning tool
Abusing Exceptions for Code Execution, Part 1

Zoom Zero Day: 4+ Million Webcams & maybe an RCE? Just get them to visit your website!, by Jonathan Leitschuh
Abusing Exceptions for Code Execution, Part 1

What is a Buffer Overflow, Attack Types and Prevention Methods

Epigenetics - Wikipedia

Ransomware - Definition
Recomendado para você
-
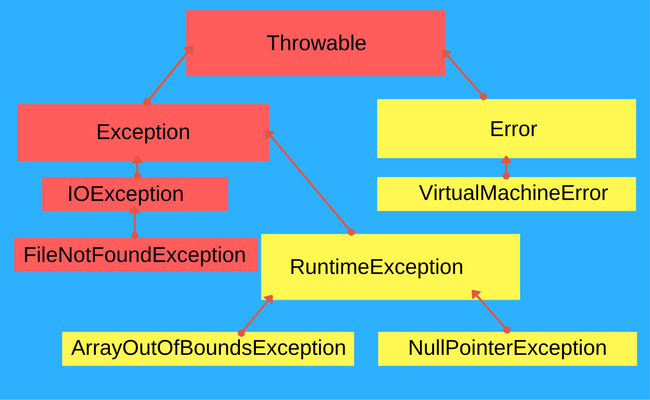
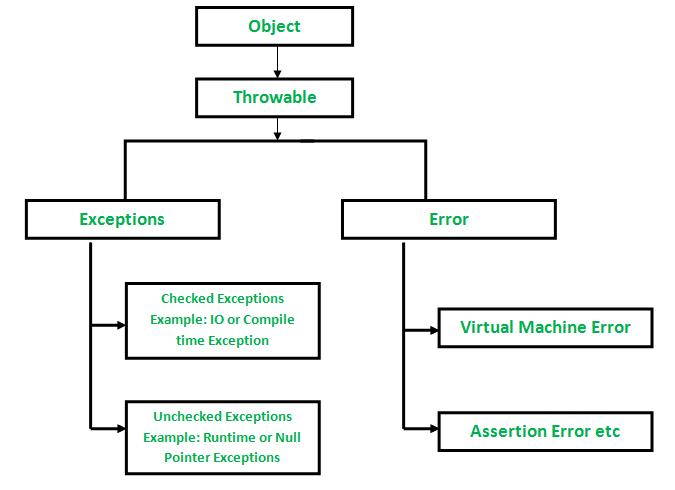 Checked vs Unchecked Exceptions in Java - GeeksforGeeks19 setembro 2024
Checked vs Unchecked Exceptions in Java - GeeksforGeeks19 setembro 2024 -
 Java Fundamentals Tutorial: Exceptions19 setembro 2024
Java Fundamentals Tutorial: Exceptions19 setembro 2024 -
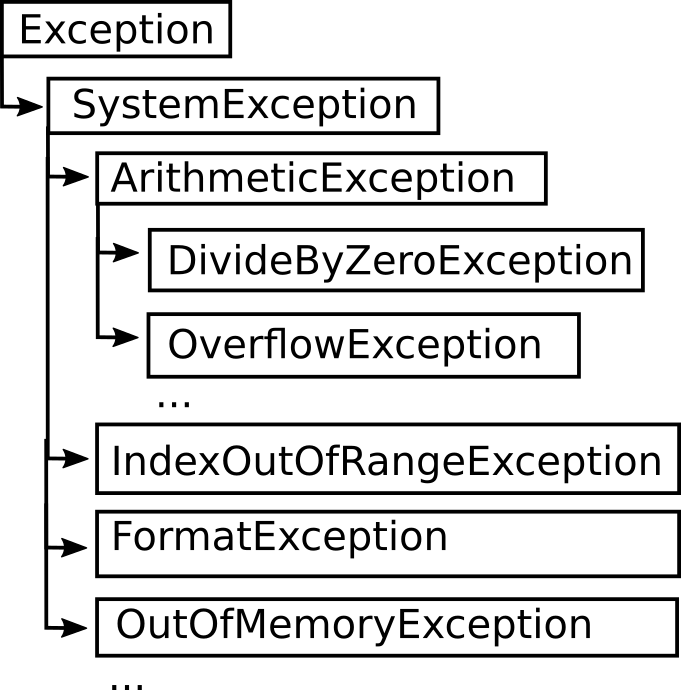
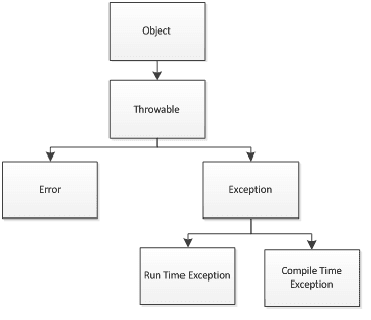 Types of Exceptions - w3resource19 setembro 2024
Types of Exceptions - w3resource19 setembro 2024 -
Hierarchy of exceptions - Hyperskill19 setembro 2024
-
 How to Throw Exceptions (The Java™ Tutorials > Essential Java Classes > Exceptions)19 setembro 2024
How to Throw Exceptions (The Java™ Tutorials > Essential Java Classes > Exceptions)19 setembro 2024 -
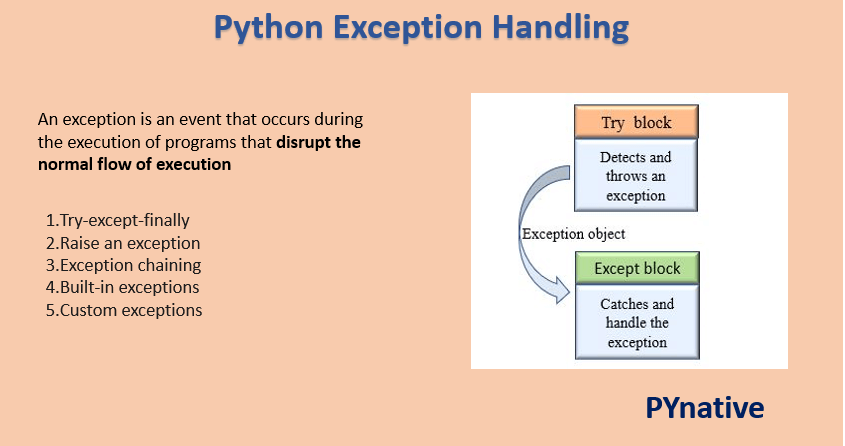 Python Exceptions and Errors – PYnative19 setembro 2024
Python Exceptions and Errors – PYnative19 setembro 2024 -
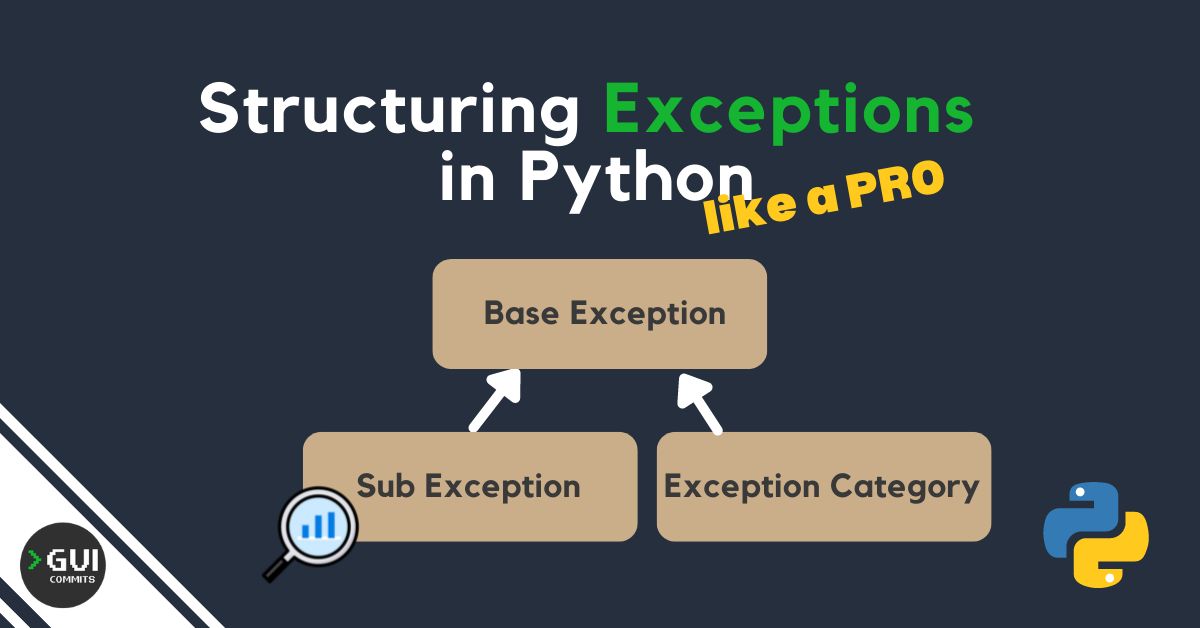 Structuring exceptions in Python like a PRO 🐍 🏗️ 💣19 setembro 2024
Structuring exceptions in Python like a PRO 🐍 🏗️ 💣19 setembro 2024 -
 Reading 5, Part 2: Exceptions19 setembro 2024
Reading 5, Part 2: Exceptions19 setembro 2024 -
 11 Mistakes Java Developers Make When Using Exceptions, by Rafael Chinelato Del Nero19 setembro 2024
11 Mistakes Java Developers Make When Using Exceptions, by Rafael Chinelato Del Nero19 setembro 2024 -
 Exceptions in Snowflake Stored Procedures - ThinkETL19 setembro 2024
Exceptions in Snowflake Stored Procedures - ThinkETL19 setembro 2024
você pode gostar
-
 GTA 5 VIDA REAL - TIRO NO ENCONTRO DE CARROS REBAIXADOS! DEU POLÍCIA e T19 setembro 2024
GTA 5 VIDA REAL - TIRO NO ENCONTRO DE CARROS REBAIXADOS! DEU POLÍCIA e T19 setembro 2024 -
 Programa de Dança Experimental – UFMG PRODAEX- Programa de Dança Experimenal19 setembro 2024
Programa de Dança Experimental – UFMG PRODAEX- Programa de Dança Experimenal19 setembro 2024 -
 Wise mystical tree meme explained|Búsqueda de TikTok19 setembro 2024
Wise mystical tree meme explained|Búsqueda de TikTok19 setembro 2024 -
 Three-dimensional xadrez de Star Trek - AliExpress19 setembro 2024
Three-dimensional xadrez de Star Trek - AliExpress19 setembro 2024 -
 Farmers' Almanac Releases Summer 2023 Weather Forecast - Farmers' Almanac - Plan Your Day. Grow Your Life.19 setembro 2024
Farmers' Almanac Releases Summer 2023 Weather Forecast - Farmers' Almanac - Plan Your Day. Grow Your Life.19 setembro 2024 -
 Lionel Messi PSG jersey revenue: How much have PSG earned so far?19 setembro 2024
Lionel Messi PSG jersey revenue: How much have PSG earned so far?19 setembro 2024 -
 Jogo de futebol ps4 +189 anúncios na OLX Brasil19 setembro 2024
Jogo de futebol ps4 +189 anúncios na OLX Brasil19 setembro 2024 -
Download Roblox for android 4.2.219 setembro 2024
-
 Minecraft 2d artist pixel art19 setembro 2024
Minecraft 2d artist pixel art19 setembro 2024 -
 Is 'Final Fantasy 7' on Xbox One? How to play the game that19 setembro 2024
Is 'Final Fantasy 7' on Xbox One? How to play the game that19 setembro 2024