Windows Command-Line Obfuscation
Por um escritor misterioso
Last updated 16 setembro 2024
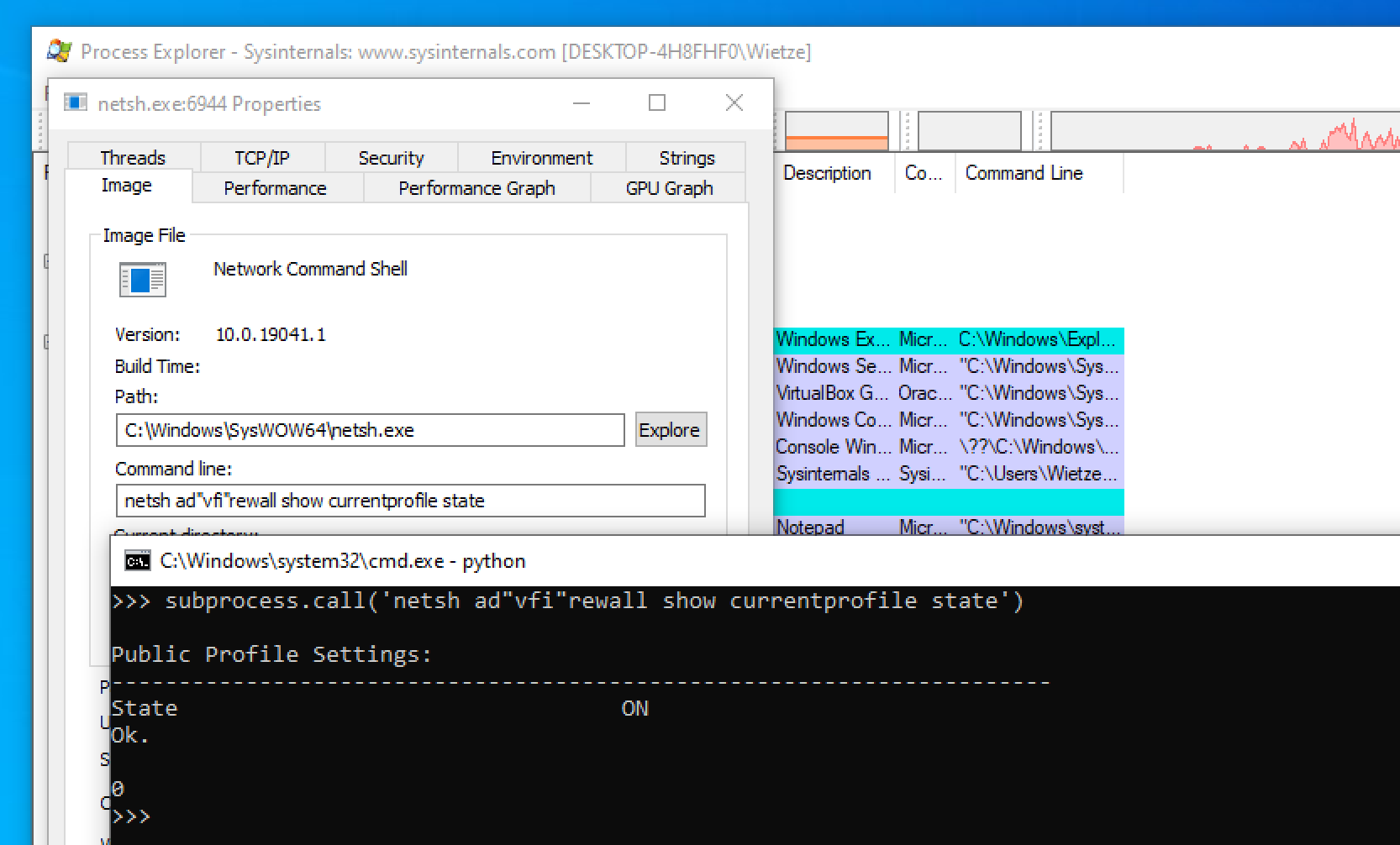
Many Windows applications have multiple ways in which the same command line can be expressed, usually for compatibility or ease-of-use reasons. As a result, command-line arguments are implemented inconsistently making detecting specific commands harder due to the number of variations. This post shows how more than 40 often-used, built-in Windows applications are vulnerable to forms of command-line obfuscation, and presents a tool for analysing other executables.
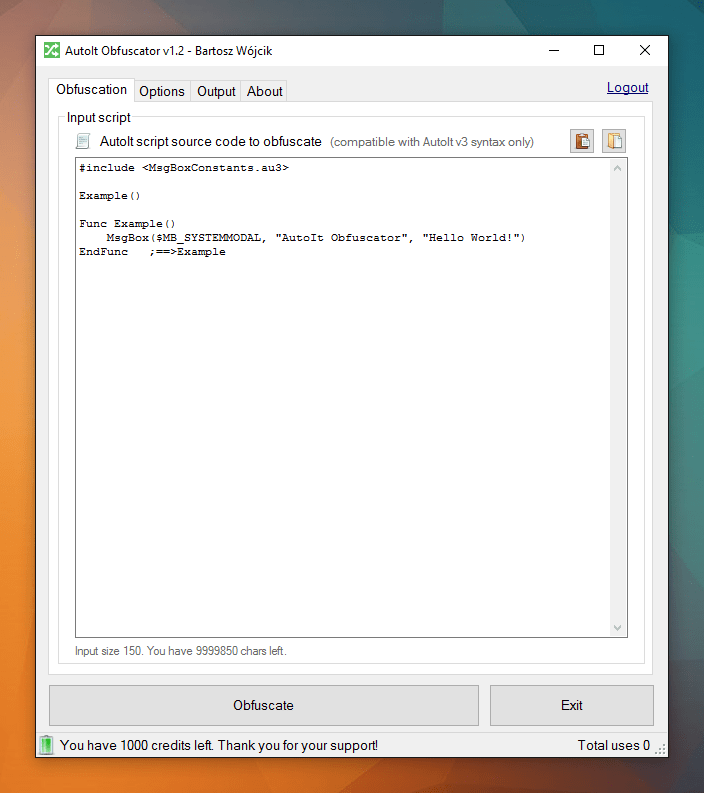
Obfuscate AutoIt scripts from Python code - DEV Community

Commandline Obfusaction - Red Team Notes

The Invoke-Obfuscation Usage Guide :: Part 2 — Daniel Bohannon
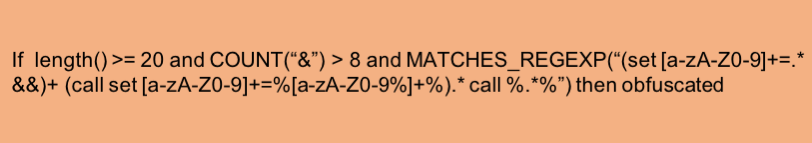
Obfuscated Command Line Detection Using Machine Learning - REAL

Detecting Obfuscated Command-lines with a Large Language Model
hacking-material-books/obfuscation/simple_obfuscation.md at master
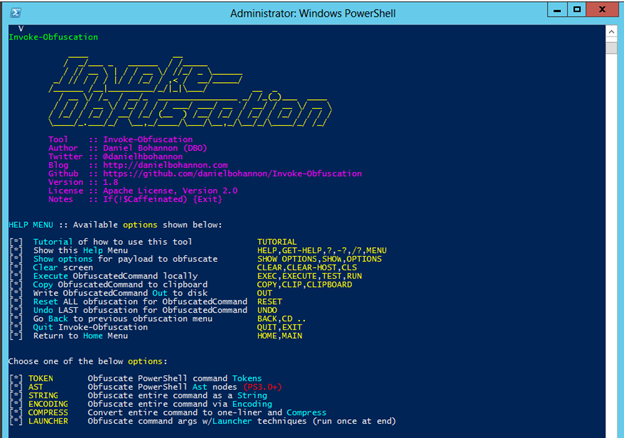
Invoke-Obfuscation — Hiding Payloads To Avoid Detection
Windows Red Team Defense Evasion Techniques

Exploring Windows Command-Line Obfuscation
GitHub - wietze/windows-command-line-obfuscation: Project for
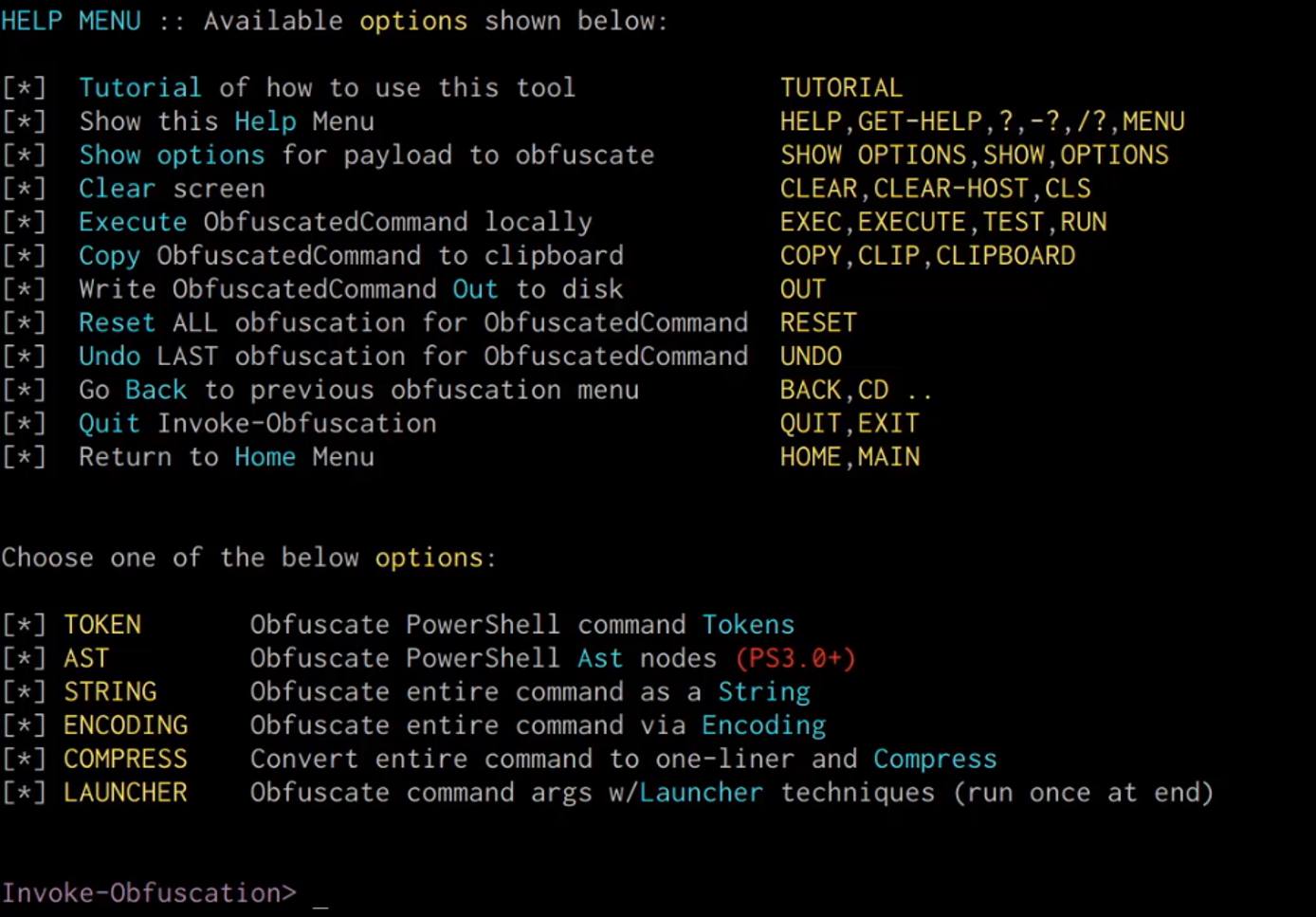
PowerShell Obfuscation using SecureString
Recomendado para você
-
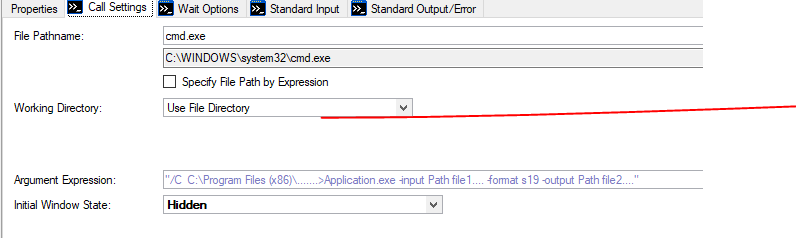
 Executing Command Prompt commands in SSIS – SQL Server Rider16 setembro 2024
Executing Command Prompt commands in SSIS – SQL Server Rider16 setembro 2024 -
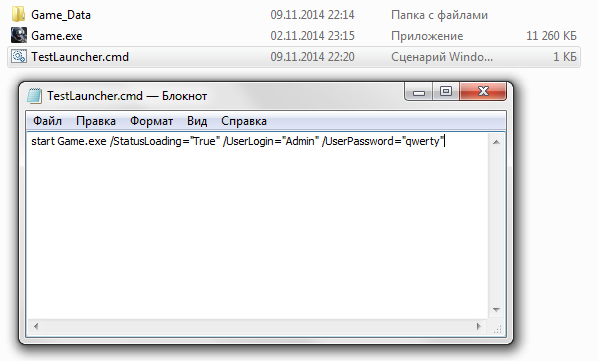
 How can I run an application with arguments from Windows Explorer? - Super User16 setembro 2024
How can I run an application with arguments from Windows Explorer? - Super User16 setembro 2024 -
 cmd - How do i run a program with arguments and as administrator16 setembro 2024
cmd - How do i run a program with arguments and as administrator16 setembro 2024 -
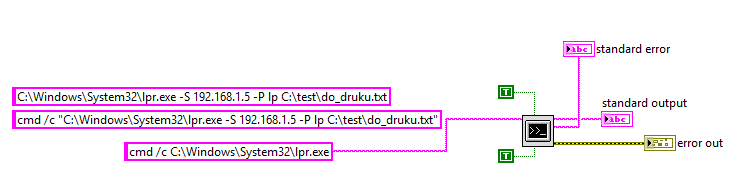
Passing arguments to exe using the Argument Expression - NI Community16 setembro 2024
-
 Command line arguments to PC Project.EXE ? - Unity Forum16 setembro 2024
Command line arguments to PC Project.EXE ? - Unity Forum16 setembro 2024 -
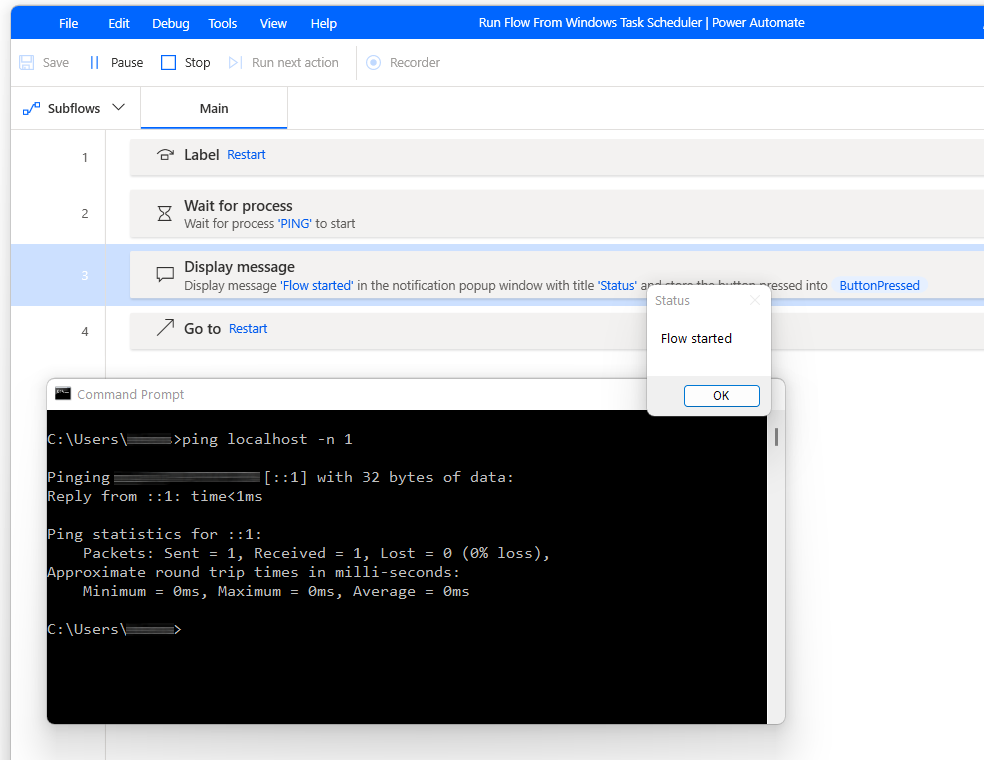 Run Flow From Command Prompt or Windows Task Scheduler16 setembro 2024
Run Flow From Command Prompt or Windows Task Scheduler16 setembro 2024 -
 System Exec - not possible to recognize program or batch file16 setembro 2024
System Exec - not possible to recognize program or batch file16 setembro 2024 -
 File:Microsoft Windows CE Version 3.0 (Build 126) cmd.exe Command16 setembro 2024
File:Microsoft Windows CE Version 3.0 (Build 126) cmd.exe Command16 setembro 2024 -
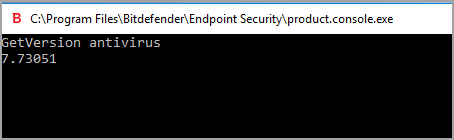
 executable - How can I find out if an .EXE has Command-Line16 setembro 2024
executable - How can I find out if an .EXE has Command-Line16 setembro 2024 -
 Using the command line interface16 setembro 2024
Using the command line interface16 setembro 2024
você pode gostar
-
 🏆 7 MEJORES JUEGOS para JUGAR con AMIGOS ONLINE u/o LAN✓ / JUEGOS DE BAJOS RECURSOS ⚡ 2022 - CENTRODEAPP16 setembro 2024
🏆 7 MEJORES JUEGOS para JUGAR con AMIGOS ONLINE u/o LAN✓ / JUEGOS DE BAJOS RECURSOS ⚡ 2022 - CENTRODEAPP16 setembro 2024 -
 Shunsuke Yoshino, Sanrio Boys Wiki16 setembro 2024
Shunsuke Yoshino, Sanrio Boys Wiki16 setembro 2024 -
 Chess.com on X: Don't rush today's puzzle, you might miss something! 🧩 Can you find the win as White? 🧐 / X16 setembro 2024
Chess.com on X: Don't rush today's puzzle, you might miss something! 🧩 Can you find the win as White? 🧐 / X16 setembro 2024 -
 Kit Garfo Inox 12 Peças 19cm TOP ÚTIL - TOP0998 Mirão16 setembro 2024
Kit Garfo Inox 12 Peças 19cm TOP ÚTIL - TOP0998 Mirão16 setembro 2024 -
 I think Black Clover Opening 4 Guess who's Back reference this16 setembro 2024
I think Black Clover Opening 4 Guess who's Back reference this16 setembro 2024 -
IShowSpeed Finally met Cristiano Ronaldo. #ishowspeed #speed #ronaldo16 setembro 2024
-
 have you heard about Billlie? — tsuki twitter update16 setembro 2024
have you heard about Billlie? — tsuki twitter update16 setembro 2024 -
 White Satin Jumpsuit by Ieena for Mac Duggal for $5416 setembro 2024
White Satin Jumpsuit by Ieena for Mac Duggal for $5416 setembro 2024 -
 The Last Guardian Wiki – Everything you need to know about the game16 setembro 2024
The Last Guardian Wiki – Everything you need to know about the game16 setembro 2024 -
Blue Spring Ride Page. 2 - Watch on Crunchyroll16 setembro 2024